End Point Management Software is a crucial tool for businesses looking to streamline device management and bolster cybersecurity. In this detailed exploration, we dive into the key features, implementation steps, and security benefits of this software, shedding light on its significance in today’s digital landscape.
Definition of End Point Management Software
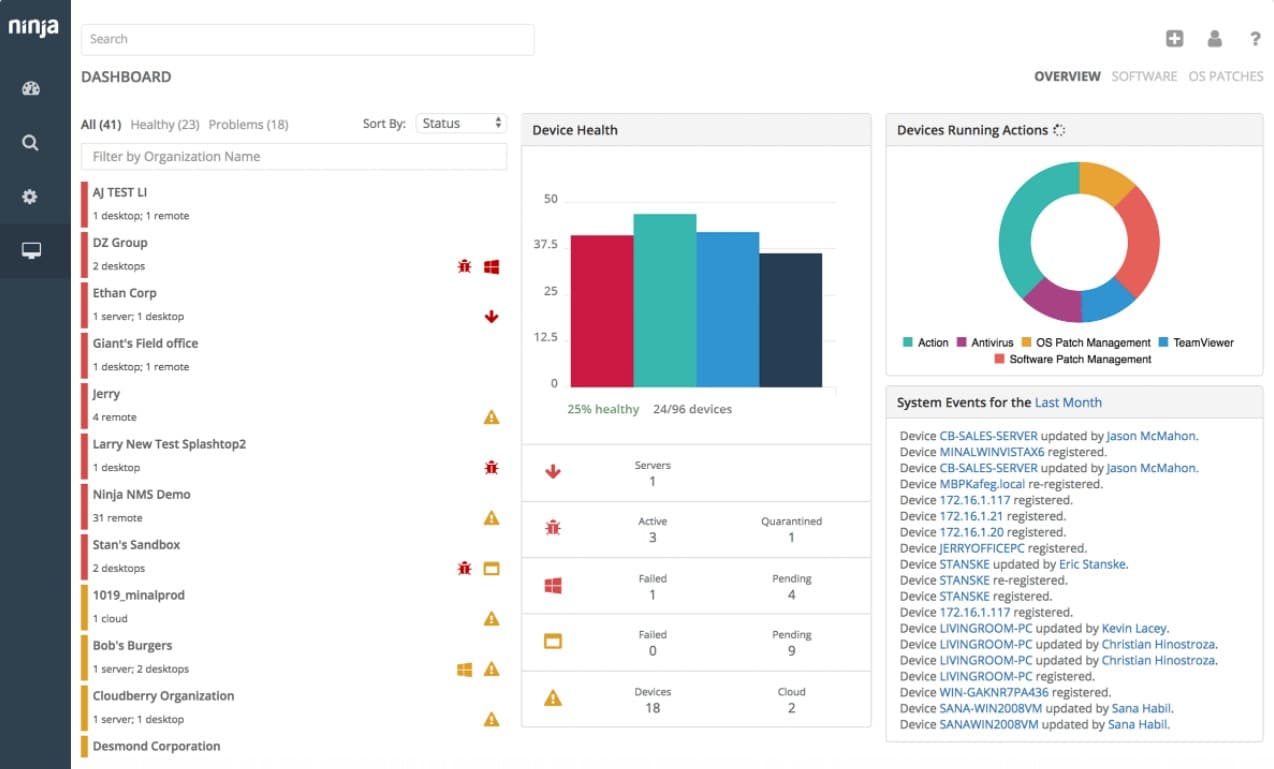
End Point Management Software refers to a centralized solution used by organizations to manage, secure, and monitor end-user devices such as laptops, desktops, smartphones, and tablets. This software allows IT teams to control and optimize the performance, security, and compliance of these devices from a single console.
Examples of Popular End Point Management Software
- Microsoft Intune: A cloud-based endpoint management solution that provides mobile device management, mobile application management, and PC management capabilities.
- VMware Workspace ONE: Offers unified endpoint management for managing and securing all endpoints in an organization, including mobile, desktop, and IoT devices.
- IBM BigFix: Provides endpoint management, patch management, security configuration management, and compliance capabilities for heterogeneous IT environments.
The Importance of Implementing End Point Management Software for Businesses
Implementing End Point Management Software is crucial for businesses due to the following reasons:
- Enhanced Security: Ensures all devices are up-to-date with security patches and compliance requirements, reducing the risk of cyber threats and data breaches.
- Improved Efficiency: Streamlines device management processes, automates routine tasks, and reduces IT workload, leading to increased productivity.
- Cost Savings: Helps in optimizing device usage, reducing downtime, and minimizing support costs, resulting in overall cost savings for the organization.
- Compliance Management: Enables organizations to enforce security policies, track device usage, and ensure regulatory compliance across all endpoints.
Features of End Point Management Software
Endpoint management software comes with a variety of features designed to help organizations secure and manage end user devices efficiently. These key features play a crucial role in ensuring that devices are properly maintained, monitored, and protected from potential security threats.
Device Inventory Management, End point management software
- Automated device discovery and inventory tracking
- Centralized view of all devices connected to the network
- Real-time updates on device status and configurations
Software Deployment and Updates
- Remote deployment of software applications and updates
- Scheduling of software patches and updates for minimal disruption
- Ensuring all devices are running the latest software versions for security compliance
Security Management
- Endpoint protection against malware, viruses, and other cyber threats
- Implementation of security policies and enforcement of compliance
- Monitoring of security incidents and immediate response to threats
Remote Troubleshooting and Support
- Remote access to end user devices for troubleshooting and issue resolution
- Support for help desk personnel to diagnose and fix device-related problems
- Reduced downtime and increased productivity through quick resolution of issues
Implementation of End Point Management Software

Implementing end point management software in an organization involves several key steps to ensure a smooth deployment and effective utilization of the software. By following best practices and being prepared to address common challenges, organizations can maximize the benefits of end point management software.
Key Steps in Implementing End Point Management Software
- Assessing Current Infrastructure: Evaluate the existing IT environment to determine compatibility and integration requirements for the end point management software.
- Setting Clear Objectives: Define specific goals and outcomes that the organization aims to achieve through the implementation of the software.
- Choosing the Right Solution: Select an end point management software that aligns with the organization’s needs and can effectively address its unique challenges.
- Planning Deployment: Develop a detailed deployment plan that Artikels timelines, responsibilities, and potential risks to ensure a successful rollout.
- Training and Support: Provide adequate training to IT staff and end users to facilitate smooth adoption and utilization of the software.
Best Practices for Deploying End Point Management Software
- Engage Stakeholders: Involve key stakeholders from different departments in the planning and implementation process to ensure alignment with organizational goals.
- Start Small: Begin with a pilot deployment in a limited environment to test functionality and identify any potential issues before scaling up.
- Monitor Performance: Continuously monitor the performance of the software post-deployment to identify areas for improvement and optimize its usage.
- Regular Updates: Stay up-to-date with software updates and patches to ensure security and functionality are maintained at all times.
Common Challenges and How to Overcome Them
- Resistance to Change: Address resistance through effective communication, training, and highlighting the benefits of the software for all stakeholders.
- Integration Issues: Conduct thorough testing and work closely with vendors to resolve any integration challenges during the implementation process.
- Security Concerns: Implement robust security measures and protocols to safeguard sensitive data and ensure compliance with industry regulations.
- Resource Constraints: Allocate sufficient resources, both in terms of budget and manpower, to support the implementation and ongoing maintenance of the software.
Security Benefits of End Point Management Software
Endpoint management software plays a crucial role in enhancing cybersecurity for organizations by providing comprehensive security measures to protect endpoints such as laptops, desktops, mobile devices, and servers. This software helps in securing the network infrastructure and data by enforcing security policies, detecting and preventing security threats, and ensuring compliance with security standards.
Enhanced Security Measures
- Endpoint Protection: End point management software offers advanced endpoint protection capabilities such as antivirus, anti-malware, and firewall to safeguard endpoints from cyber threats.
- Security Patch Management: It ensures that all endpoints are up to date with the latest security patches and updates to prevent vulnerabilities exploitation.
- Data Encryption: End point management software enables data encryption on endpoints to protect sensitive information from unauthorized access.
- Device Control: It allows organizations to control and monitor the usage of devices connected to endpoints, preventing data leakage and unauthorized access.
Prevention of Security Breaches
- Malware Attacks: End point management software helps in detecting and blocking malware attacks, preventing the installation of malicious software on endpoints.
- Ransomware Attacks: By implementing security measures such as endpoint protection and data encryption, organizations can prevent ransomware attacks that encrypt data and demand ransom.
- Phishing Attacks: End point management software can identify and block phishing attempts that aim to steal sensitive information through deceptive emails or websites.
- Unauthorized Access: With device control features, organizations can prevent unauthorized access to endpoints and ensure that only authorized users can access sensitive data.
Conclusion

As we wrap up our discussion on End Point Management Software, it’s evident that this technology plays a vital role in safeguarding organizations and optimizing operational processes. With its array of features and security enhancements, embracing this software is a strategic move for any modern business.
Key Questions Answered
How does End Point Management Software improve cybersecurity?
End Point Management Software enhances cybersecurity by providing centralized control over end user devices, allowing for efficient monitoring and enforcement of security protocols.
What are some common challenges during the implementation of End Point Management Software?
Common challenges include compatibility issues with existing systems, resistance from employees to new processes, and ensuring seamless integration across all devices.
Can End Point Management Software prevent security breaches?
Yes, End Point Management Software can prevent security breaches by implementing proactive security measures, enforcing compliance policies, and swiftly addressing potential vulnerabilities.
