Endpoint protection software sets the stage for this enthralling narrative, offering readers a glimpse into a story that is rich in detail and brimming with originality from the outset. In today’s digital landscape, safeguarding endpoints is paramount, and this software plays a crucial role in ensuring comprehensive security measures.
As we delve deeper into the realm of endpoint protection software, we uncover its significance, various types, key components, best practices for implementation, and evaluation criteria to make informed decisions in enhancing cybersecurity.
Introduction to Endpoint Protection Software
Endpoint protection software is a crucial cybersecurity solution designed to safeguard endpoints, such as laptops, desktops, mobile devices, and servers, from potential security threats.
Using endpoint protection software is essential in today’s digital landscape, where cyber threats are becoming more sophisticated and prevalent. It helps organizations prevent, detect, and respond to various types of cyber attacks, including malware, ransomware, phishing, and zero-day exploits.
Key Features of Endpoint Protection Software
- Real-time Threat Detection and Prevention: Endpoint protection software continuously monitors for suspicious activities and blocks potential threats in real-time.
- Advanced Anti-Malware Capabilities: It includes antivirus and anti-malware features to protect endpoints from malicious software.
- Firewall and Intrusion Detection: Helps in preventing unauthorized access to endpoints through network monitoring and intrusion detection.
- Device Control and Data Encryption: Allows organizations to control device access and encrypt sensitive data to prevent data breaches.
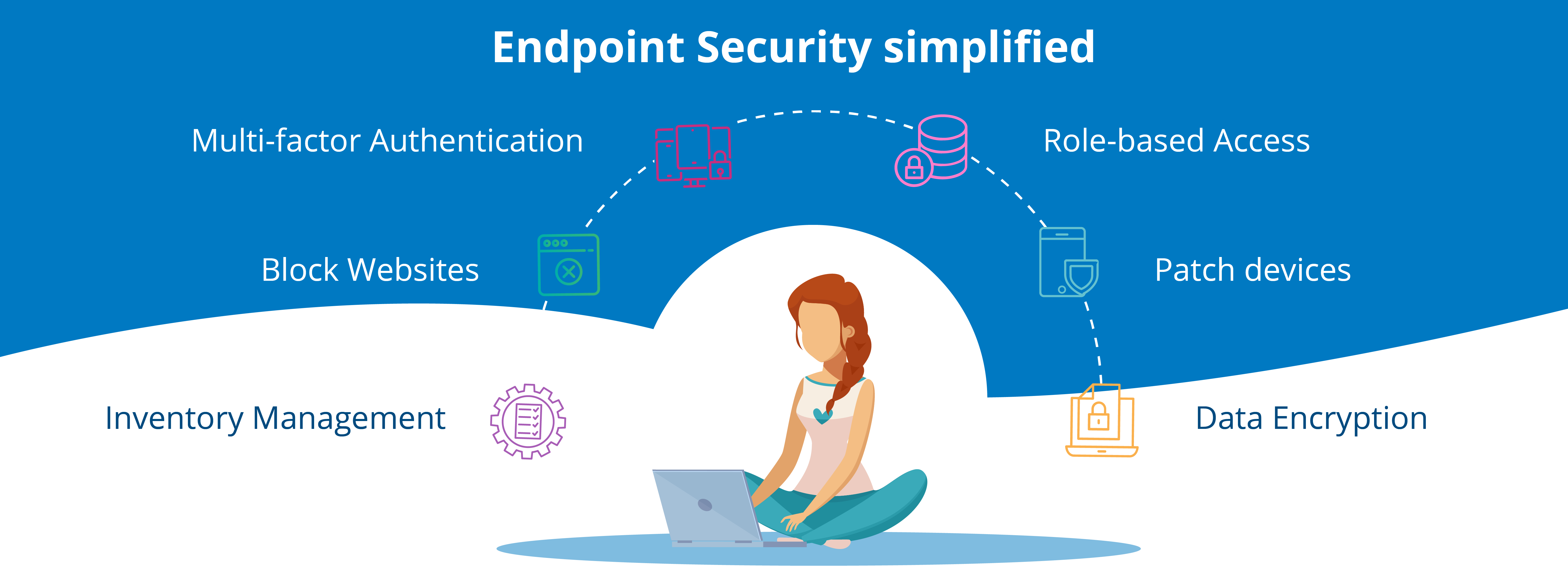
- Centralized Management Console: Provides a single interface for managing security policies, monitoring endpoints, and generating reports.
Types of Endpoint Protection Software
Endpoint protection software comes in various types, each serving a specific purpose in safeguarding devices and networks from cyber threats. Let’s explore the different types and their characteristics.
Antivirus Software
Antivirus software is designed to detect, prevent, and remove malicious software like viruses, worms, and Trojans from infecting endpoints. It typically scans files and programs for known malware signatures and behavior patterns to block or quarantine threats.
Anti-Malware Software
Anti-malware software goes beyond traditional antivirus programs by targeting a wider range of malicious software, including spyware, adware, and ransomware. It provides real-time protection against evolving threats and often includes features like email scanning and web protection.
Firewalls
Firewalls act as a barrier between an endpoint device and the internet, monitoring and controlling incoming and outgoing network traffic. They can block unauthorized access attempts, filter out malicious content, and prevent attacks like denial-of-service (DoS) and distributed denial-of-service (DDoS).
Cloud-Based vs. On-Premise Solutions
Cloud-based endpoint protection solutions store data and perform security operations in the cloud, offering scalability, automatic updates, and reduced hardware requirements. On the other hand, on-premise solutions require local installation and management, providing greater control over security policies and data privacy.
Advantages and Disadvantages
- Cloud-Based: Advantages include easier deployment, centralized management, and continuous updates. However, potential disadvantages may include dependency on internet connectivity and concerns about data security and privacy.
- On-Premise: Advantages include full control over security configurations, data sovereignty, and offline protection. Yet, drawbacks may include higher upfront costs, maintenance overhead, and slower response to new threats.
Key Components of Endpoint Protection Software
Endpoint protection software is composed of several key components that work together to ensure the security of endpoints within a network. Each component plays a vital role in defending against various cyber threats and safeguarding sensitive data.
Real-Time Scanning
Real-time scanning is a crucial feature of endpoint protection software that continuously monitors files and processes on endpoints for any signs of malicious activity. This component helps in detecting and blocking threats in real-time, preventing potential security breaches before they can cause harm.
- Scans files and applications in real-time to identify and eliminate malware.
- Monitors network traffic for suspicious behavior and potential threats.
- Provides immediate alerts and notifications to administrators when threats are detected.
Threat Intelligence
Threat intelligence is another essential component that enriches endpoint protection software with up-to-date information on emerging cyber threats and vulnerabilities. By leveraging threat intelligence feeds and databases, this component enhances the software’s ability to detect and respond to new and evolving security risks.
- Utilizes threat feeds and databases to stay informed about the latest malware strains and attack techniques.
- Enhances threat detection capabilities by correlating threat intelligence with endpoint activity.
- Helps in prioritizing and addressing high-risk threats based on their severity and impact.
Behavior Monitoring
Behavior monitoring is a proactive component of endpoint protection software that focuses on analyzing and identifying anomalous behavior patterns on endpoints. By monitoring endpoint activities and behaviors, this component can detect suspicious actions that may indicate a potential security threat.
- Tracks user behavior and system activities to identify deviations from normal patterns.
- Detects and blocks malicious activities such as unauthorized access attempts and data exfiltration.
- Provides insights into potential security incidents and helps in responding promptly to mitigate risks.
Implementation and Best Practices
Implementing endpoint protection software involves several key steps to ensure the security of devices and networks. It is essential to follow best practices for configuring and managing endpoint protection solutions effectively. Additionally, strategies must be in place to maintain endpoint security across diverse devices and networks.
Steps for Implementing Endpoint Protection Software
- Conduct a thorough assessment of the organization’s existing IT infrastructure and security protocols.
- Choose the right endpoint protection software based on the specific needs and requirements of the organization.
- Develop a comprehensive implementation plan that includes timelines, responsibilities, and resources.
- Deploy the endpoint protection software across all devices and networks within the organization.
- Regularly monitor and update the software to ensure it remains effective against evolving threats.
Best Practices for Configuring and Managing Endpoint Protection Solutions
- Enable real-time scanning and automatic updates to detect and respond to threats promptly.
- Implement strong password policies and multi-factor authentication to enhance security measures.
- Regularly backup data to prevent data loss in case of a security breach.
- Restrict administrative privileges to minimize the risk of unauthorized access to critical systems.
- Conduct regular security training and awareness programs for employees to educate them on best practices.
Strategies for Ensuring Endpoint Security Across Diverse Devices and Networks
- Implement network segmentation to isolate sensitive data and devices from potential threats.
- Use encryption to protect data in transit and at rest, especially on mobile devices and remote connections.
- Implement endpoint detection and response (EDR) solutions to proactively detect and respond to advanced threats.
- Monitor and analyze endpoint activity to identify anomalies and potential security breaches.
- Regularly audit and assess the organization’s endpoint security posture to identify and address vulnerabilities.
Endpoint Protection Software Evaluation
When evaluating the effectiveness of endpoint protection software, there are several key criteria to consider. It’s important to compare different solutions based on performance, ease of use, and scalability to ensure that your organization’s endpoints are adequately protected. Regular testing and updates are also crucial to maintain the security of your endpoints.
Performance
- Look for endpoint protection software that offers real-time monitoring and threat detection to swiftly identify and respond to potential security incidents.
- Consider the impact of the software on system performance to ensure that it does not slow down endpoint devices.
- Check for independent test results and reviews to gauge the effectiveness of the software in protecting against known and emerging threats.
Ease of Use
- Choose a solution that is easy to deploy and manage, with a user-friendly interface that simplifies security configuration and monitoring.
- Look for endpoint protection software that offers centralized management capabilities to streamline security operations across all endpoints.
- Consider the availability of training and support resources to ensure that your team can effectively utilize the software.
Scalability, Endpoint protection software
- Assess whether the endpoint protection software can easily scale to accommodate the growth of your organization and the increasing number of endpoints.
- Consider the flexibility of the software to adapt to different endpoint environments and configurations.
- Look for solutions that offer cloud-based deployment options for scalability and ease of management.
Regular Testing and Updates
- Regularly test the effectiveness of your endpoint protection software through simulated attack scenarios and penetration testing.
- Ensure that the software receives timely updates and patches to address new vulnerabilities and enhance security capabilities.
- Implement a proactive approach to security by staying informed about the latest threats and trends in endpoint security.
Final Review

In conclusion, endpoint protection software emerges as a cornerstone in the realm of cybersecurity, providing robust defense mechanisms for endpoints against evolving threats. By understanding its nuances and adopting best practices, organizations can fortify their security posture and navigate the digital landscape with confidence.
FAQ Overview: Endpoint Protection Software
What sets endpoint protection software apart from traditional antivirus programs?
Endpoint protection software offers a comprehensive approach by combining various security features like firewall protection, anti-malware tools, and behavior monitoring to secure endpoints beyond what traditional antivirus software can provide.
How does cloud-based endpoint protection differ from on-premise solutions?
Cloud-based endpoint protection operates through a cloud infrastructure, offering scalability and accessibility advantages, while on-premise solutions require local installation and maintenance, providing greater control over security measures.
Why is regular testing and updates crucial for endpoint protection software?
Regular testing and updates ensure that the software can effectively combat new and emerging threats, patch vulnerabilities, and maintain optimal performance to uphold the security of endpoints.
